GSNA Exam Questions - Online Test
GSNA Premium VCE File

150 Lectures, 20 Hours

Our pass rate is high to 98.9% and the similarity percentage between our GSNA study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the GIAC GSNA exam in just one try? I am currently studying for the GIAC GSNA exam. Latest GIAC GSNA Test exam practice questions and answers, Try GIAC GSNA Brain Dumps First.
Also have GSNA free dumps questions for you:
NEW QUESTION 1
Which of the following features of a switch helps to protect network from MAC flood and MAC spoofing?
- A. Multi-Authentication
- B. Port security
- C. MAC Authentication Bypass
- D. Quality of Service (QoS)
Answer: B
Explanation:
If a switch has the ability to enable port security, this will help to protect network from both the MAC Flood and MAC Spoofing attacks. Answer D is incorrect. Quality of Service (QoS) feature is useful for prioritizing VOIP traffic. Switches are offering the ability to assign a device a Quality of Service (QoS) value or a rate limiting value based on the RADIUS response. Answer A is incorrect. Multi-Authentication feature is used to allow multiple devices to use a single port. Answer C is incorrect. MAC Authentication Bypass feature is used to allow the RADIUS server to specify the default VLAN/ACL for every device that doesn't authenticate by 802.1X.
NEW QUESTION 2
You work as a professional Ethical Hacker. You are assigned a project to test the security of www.we-are-secure.com. You are working on the Windows Server 2003 operating system. You suspect that your friend has installed the keyghost keylogger onto your computer. Which of the following countermeasures would you employ in such a situation?
- A. Use commercially available anti-keyloggers such as PrivacyKeyboard.
- B. Use on-screen keyboards and speech-to-text conversion software which can also be useful against keyloggers, as there are no typing or mouse movements involved.
- C. Remove the SNMP agent or disable the SNMP service.
- D. Monitor the programs running on the server to see whether any new process is runningon the server or not.
Answer: ABD
Explanation:
It is very hard to detect a keylogger's activity. Hence, a Network Administrator should take the following steps as countermeasures against software keyloggers: Actively monitor the programs running on the server. Monitor the network whenever an application attempts to make a network connection. Use commercially available anti-keyloggers, such as PrivacyKeyboard. Update one's antivirus regularly. Use on-screen keyboards and speech-to-text conversion software which can also be useful against keyloggers, as there are no typing or mouse movements involved.
Answer C is incorrect. An SNMP service is not used for keystroke logging. Hence, removing an SNMP agent may be a valid option if, and only if, the server is vulnerable to SNMP enumeration.
NEW QUESTION 3
John visits an online shop that stores the IDs and prices of the items to buy in a cookie. After selecting the items that he wants to buy, the attacker changes the price of the item to
* 1. Original cookie values: ItemID1=2 ItemPrice1=900 ItemID2=1 ItemPrice2=200 Modified cookie values: ItemID1=2 ItemPrice1=1 ItemID2=1 ItemPrice2=1 Now, he clicks the Buy button, and the prices are sent to the server that calculates the total price. Which of the following hacking techniques is John performing?
- A. Cross site scripting
- B. Man-in-the-middle attack
- C. Cookie poisoning
- D. Computer-based social engineering
Answer: C
Explanation:
John is performing cookie poisoning. In cookie poisoning, an attacker modifies the value of cookies before sending them back to the server. On modifying the cookie values, an attacker can log in to any other user account and can perform identity theft. The following figure explains how cookie poisoning occurs: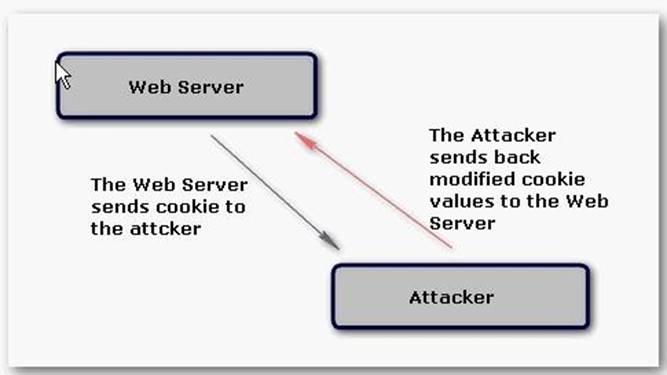
For example: The attacker visits an online shop that stores the IDs and prices of the items to buy in a cookie. After selecting the items that he wants to buy, the attacker changes the price of the item to 1. Original cookie values: ItemID1= 2 ItemPrice1=900 ItemID2=1 ItemPrice2=200 Modified cookie values: ItemID1= 2 ItemPrice1=1 ItemID2=1 ItemPrice2=1 Now, the attacker clicks the Buy button and the prices are sent to the server that calculates the total price. Another use of a Cookie Poisoning attack is to pretend to be another user after changing the username in the cookie values: Original cookie values: LoggedIn= True Username = Mark Modified cookie values: LoggedIn= True Username = Admin Now, after modifying the cookie values, the attacker can do the admin login.
Answer A is incorrect. A cross site scripting attack is one in which an attacker enters malicious data into a Website. For example, the attacker posts a message that contains malicious code to any newsgroup site. When another user views this message, the browser interprets this code and executes it and, as a result, the attacker is able to take control of the user's system. Cross site scripting attacks require the execution of client-side languages such as JavaScript, Java, VBScript, ActiveX, Flash, etc. within a user's Web environment. With the help of a cross site scripting attack, the attacker can perform cookie stealing, sessions hijacking, etc.
NEW QUESTION 4
You work as a Network Administrator for XYZ CORP. The company has a Windows-based network. You are concerned about the vulnerabilities existing in the network of the company. Which of the following can be a cause for making the network vulnerable? (Choose two)
- A. Use of well-known code
- B. Use of uncommon code
- C. Use of uncommon software
- D. Use of more physical connections
Answer: AD
Explanation:
In computer security, the term vulnerability is a weakness which allows an attacker to reduce a system's Information Assurance. A computer or a network can be vulnerable due to the following reasons: Complexity: Large, complex systems increase the probability of flaws and unintended access points. Familiarity: Using common, well-known code, software, operating systems, and/or hardware increases the probability an attacker has or can find the knowledge and tools to exploit the flaw. Connectivity: More physical connections, privileges, ports, protocols, and services and time each of those are accessible increase vulnerability. Password management flaws: The computer user uses weak passwords that could be discovered by brute force. The computer user stores the password on the computer where a program can access it. Users re-use passwords between many programs and websites. Fundamental operating system design flaws: The operating system designer chooses to enforce sub optimal policies on user/program management. For example, operating systems with policies such as default permit grant every program and every user full access to the entire computer. This operating system flaw allows viruses and malware to execute commands on behalf of the administrator. Internet Website Browsing: Some Internet websites may contain harmful Spyware or Adware that can be installed automatically on the computer systems. After visiting those websites, the computer systems become infected and personal information will be collected and passed on to third party individuals. Software bugs: The programmer leaves an exploitable bug in a software program. The software bug may allow an attacker to misuse an application. Unchecked user input: The program assumes that all user input is safe. Programs that do not check user input can allow unintended direct execution of commands or SQL statements (known as Buffer overflows, SQL injection or other non-validated inputs). Answer B, C are incorrect. Use of common software and common code can make a network vulnerable.
NEW QUESTION 5
Which of the following is a type of web site monitoring that is done using web browser emulation or scripted real web browsers?
- A. Route analytics
- B. Passive monitoring
- C. Network tomography
- D. Synthetic monitoring
Answer: D
Explanation:
Synthetic monitoring is an active Web site monitoring that is done using Web browser emulation or scripted real Web browsers. Behavioral scripts (or paths) are created to simulate an action or path that a customer or end-user would take on a site. Those paths are then continuously monitored at specified intervals for availability and response time measures. Synthetic monitoring is valuable because it enables a Webmaster to identify problems and determine if his Web site or Web application is slow or experiencing downtime before that problem affects actual end-users or customers. Answer B is incorrect. Passive monitoring is a technique used to analyze network traffic by capturing traffic from a network by generating a copy of that traffic. It is done with the help of a span port, mirror port, or network tap. Once the data (a stream of frames or packets) has been extracted, it can be used in many ways. Passive monitoring can be very helpful in troubleshooting performance problems once they have occurred. Passive monitoring relies on actual inbound Web traffic to take measurements, so problems can only be discovered after they have occurred. Answer A is incorrect. Route analytics is an emerging network monitoring technology specifically developed to analyze the routing protocols and structures in meshed IP networks. Their main mode of operation is to passively listen to the Layer 3 routing protocol exchanges between routers for the purposes of network discovery, mapping, real-time monitoring, and routing diagnostics. Answer C is incorrect. Network tomography is an important area of network measurement that deals with monitoring the health of various links in a network using end-to-end probes sent by agents located at vantage points in the network/Internet.
NEW QUESTION 6
You work as a Network Administrator for XYZ CORP. The company has a Linux-based network. You need to configure a firewall for the company. The firewall should be able to keep track of the state of network connections traveling across the network. Which of the following types of firewalls will you configure to accomplish the task?
- A. A network-based application layer firewall
- B. Host-based application firewall
- C. An application firewall
- D. Stateful firewall
Answer: D
Explanation:
A stateful firewall is a firewall that keeps track of the state of network connections (such as TCP streams, UDP communication) traveling across it. The firewall is programmed to distinguish legitimate packets for different types of connections. Only packets matching a known connection state will be allowed by the firewall; others will be rejected. Answer B is incorrect. A host-based application firewall can monitor any application input, output, and/or system service calls made from, to, or by an application. This is done by examining information passed through system calls instead of, or in addition to, a network stack. A host-based application firewall can only provide protection to the applications running on the same host. An example of a host-based application firewall that controls system service calls by an application is AppArmor or the Mac OS X application firewall. Host-based application firewalls may also provide network-based application firewalling. Answer A is incorrect. A network-based application layer firewall, also known as a proxy-based or reverse-proxy firewall, is a computer networking firewall that operates at the application layer of a protocol stack. Application firewalls specific to a particular kind of network traffic may be titled with the service name, such as a Web application firewall. They may be implemented through software running on a host or a stand-alone piece of network hardware. Often, it is a host using various forms of proxy servers to proxy traffic before passing it on to the client or server. Because it acts on the application layer, it may inspect the contents of the traffic, blocking specified content, such as certain websites, viruses, and attempts to exploit known logical flaws in client software. Answer C is incorrect. An application firewall is a form of firewall that controls input, output, and/or access from, to, or by an application or service. It operates by monitoring and potentially blocking the input, output, or system service calls that do not meet the configured policy of the firewall. The application firewall is typically built to monitor one or more specific applications or services (such as a web or database service), unlike a stateful network firewall, which can provide some access controls for nearly any kind of network traffic. There are two primary categories of application firewalls: Network-based application firewalls Host-based application firewalls
NEW QUESTION 7
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He begins to perform a pre-attack test before conducting an attack on the We-are-secure server. Which of the following will John perform in the pre-attack phase?
- A. Determining network range
- B. Identifying active machines
- C. Enumeration
- D. Finding open ports and applications
- E. Information gathering
Answer: ABDE
Explanation:
In the pre-attack phase, there are seven steps, which have been defined by the EC-Council, as follows: 1.Information gathering 2.Determining network range 3.Identifying active machines 4.Finding open ports and applications 5.OS fingerprinting 6.Fingerprinting services 7.Mapping the network Answer C is incorrect. In the enumeration phase, the attacker gathers information such as the network user and group names, routing tables, and Simple Network Management Protocol (SNMP) data. The techniques used in this phase are as follows: 1.Obtaining Active Directory information and identifying vulnerable user accounts 2.Discovering NetBIOS names 3.Employing Windows DNS queries 4.Establishing NULL sessions and queries
NEW QUESTION 8
Many organizations create network maps of their network system to visualize the network and understand the relationship between the end devices and the transport layer that provide services. Which of the following are the techniques used for network mapping by large organizations? Each correct answer represents a complete solution. Choose three.
- A. Route analytics
- B. Active Probing
- C. SNMP-based approaches
- D. Packet crafting
Answer: ABC
Explanation:
Many organizations create network maps of their network system. These maps can be made manually using simple tools such as Microsoft Visio, or the mapping process can be simplified by using tools that integrate auto network discovery with Network mapping. Many of the vendors from the Notable network Mappers list enable a user to do the following: Customize the maps Include one's own labels Add un-discoverable items Add background images Sophisticated mapping is used to help visualize the network and understand relationships between end devices and the transport layers that provide service. Items such as bottlenecks and root cause analysis can be easier to spot using these tools. There are three main techniques used for network mapping: SNMP-based approaches, Active Probing, and Route analytics. The SNMP-based approach retrieves data from Router and Switch MIBs in order to build the network map. The Active Probing approach relies on a series of trace route like probe packets in order to build the network map. The Route analytics approach relies on information from the routing protocols to build the network map. Each of the three approaches has advantages and disadvantages in the methods that they use. Answer D is incorrect. Packet crafting is a technique that allows probing firewall rule-sets and finding entry points into the targeted system or network. This can be done with a packet generator. A packet generator is a type of software that generates random packets or allows the user to construct detailed custom packets. Packet generators utilize raw sockets. This is useful for testing implementations of IP stacks for bugs and security vulnerabilities.
NEW QUESTION 9
You work as a Network Administrator for BetaTech Inc. You have been assigned the task of designing the firewall policy for the company. Which of the following statements is unacceptable in the 'acceptable use statement' portion of the firewall policy?
- A. The computers and their applications should be used for organizational related activities only.
- B. Computers may not be left unattended with a user account still logged on.
- C. Applications other than those supplied or approved by the company can be installed on any computer.
- D. The installed e-mail application can only be used as the authorized e-mail service.
Answer: C
Explanation:
Applications other than those supplied or approved by the company shall not be installed on any computer. Answer A, B, D are incorrect. All of these statements stand true in the 'acceptable use statement' portion of the firewall policy.
NEW QUESTION 10
You configure a wireless router at your home. To secure your home Wireless LAN (WLAN), you implement WEP. Now you want to connect your client computer to the WLAN. Which of the following is the required information that you will need to configure the client computer? (Choose two)
- A. SSID of the WLAN
- B. WEP key
- C. IP address of the router
- D. MAC address of the router
Answer: AB
Explanation:
In order to connect a client computer to a secured Wireless LAN (WLAN), you are required to provide the following information: SSID of the WLAN WEP key rticlesItemsReportsHelp
NEW QUESTION 11
You are concerned about war driving bringing hackers attention to your wireless network. What is the most basic step you can take to mitigate this risk?
- A. Implement WPA
- B. Implement WEP
- C. Don't broadcast SSID
- D. Implement MAC filtering
Answer: C
Explanation:
By not broadcasting your SSID some simple war driving tools won't detect your network. However you should be aware that there are tools that will still detect networks that are not broadcasting their SSID across your network. Answer D is incorrect. While MAC filtering may help prevent a hacker from accessing your network, it won't keep him or her from finding your network.
NEW QUESTION 12
You work as a Network Administrator for Tech Perfect Inc. The company has a Windows Active Directory-based single domain single forest network. The functional level of the forest is Windows Server 2003. The company has recently provided fifty laptops to its sales team members. You are required to configure an 802.11 wireless network for the laptops. The sales team members must be able to use their data placed at a server in a cabled network. The planned network should be able to handle the threat of unauthorized access and data interception by an unauthorized user. You are also required to prevent the sales team members from communicating directly to one another. Which of the following actions will you take to accomplish the task?
- A. Implement the open system authentication for the wireless network.
- B. Configure the wireless network to use WEP encryption for the data transmitted over a wireless network.
- C. Using group policies, configure the network to allow the wireless computers to connect to the infrastructure networks only.
- D. Implement the IEEE 802.1X authentication for the wireless network.
- E. Using group policies, configure the network to allow the wireless computers to connect to the ad hoc networks only.
Answer: BCD
Explanation:
In order to enable wireless networking, you have to install access points in various areas of your office building. These access points generate omni directional signals to broadcast network traffic. Unauthorized users can intercept these packets. Hence, security is the major concern for a wireless network. The two primary threats are unauthorized access and data interception. In order to accomplish the task, you will have to take the following steps: Using group policies, configure the network to allow the wireless computers to connect to the infrastructure networks only. This will prevent the sales team members from communicating directly to one another. Implement the IEEE 802.1X authentication for the wireless network. This will allow only authenticated users to access the network data and resources. Configure the wireless network to use WEP encryption for data transmitted over a wireless network. This will encrypt the network data packets transmitted over wireless connections. Although WEP encryption does not prevent intruders from capturing the packets, it prevents them from reading the data inside.
NEW QUESTION 13
You are the Security Consultant and you frequently do vulnerability assessments on client computers. You want to have a standardized approach that would be applicable to all of your clients when doing a vulnerability assessment. What is the best way to do this?
- A. Utilize OVAL.
- B. Create your own standard and use it with all clients.
- C. Utilize each client's security policies when doing a vulnerability assessment for that client.
- D. Utilize the Microsoft security recommendations.
Answer: A
Explanation:
Open Vulnerability Assessment Language (OVAL) is a common language for security professionals to use when checking for the presence of vulnerabilities on computer systems. OVAL provides a baseline method for performing vulnerability assessments on local computer systems. Answer D is incorrect. While Microsoft security standards will be appropriate for many of your clients, they won't help clients using Linux, Macintosh, or Unix. They also won't give you insight into checking your firewalls or routers. Answer C is incorrect. This would not fulfill the requirement of having a standardized approach applicable to all clients. B is incorrect. This would not be the best way. You should use common industry standards, like OVAL.
NEW QUESTION 14
Which of the following NFS mount options specifies whether a program using a file via an NFS connection should stop and wait for the server to come back online, if the host serving the exported file system is unavailable, or if it should report an error?
- A. intr
- B. hard or soft
- C. nfsvers=2 or nfsvers=3
- D. fsid=num
Answer: B
Explanation:
The hard or soft NFS mount options are used to specify whether a program using a file via an NFS connection should stop and wait (hard) for the server to come back online, if the host serving the exported file system is unavailable, or if it should report an error. Answer A is incorrect. The intr NFS mount option allows NFS requests to be interrupted if the server goes down or cannot be reached. Answer C is incorrect. The nfsvers=2 or nfsvers=3 NFS mount options are used to specify which version of the NFS protocol to use. Answer D is incorrect. The fsid=num NFS mount option forces the file handle and file attributes settings on the wire to be num.
NEW QUESTION 15
You work as a Network Administrator of a TCP/IP network. You are having DNS resolution problem. Which of the following utilities will you use to diagnose the problem?
- A. PING
- B. IPCONFIG
- C. TRACERT
- D. NSLOOKUP
Answer: D
Explanation:
NSLOOKUP is a tool for diagnosing and troubleshooting Domain Name System (DNS) problems. It performs its function by sending queries to the DNS server and obtaining detailed responses at the command prompt. This information can be useful for diagnosing and resolving name resolution issues, verifying whether or not the resource records are added or updated correctly in a zone, and debugging other server-related problems. This tool is installed along with the TCP/IP protocol through the Control Panel. Answer A is incorrect. The ping command-line utility is used to test connectivity with a host on a TCP/IP-based network. This is achieved by sending out a series of packets to a specified destination host. On receiving the packets, the destination host responds with a series of replies. These replies can be used to determine whether or not the network is working properly. Answer B is incorrect. IPCONFIG is a command-line utility used to display current TCP/IP network configuration values and update or release the Dynamic Host Configuration Protocol (DHCP) allocated leases. It is also used to display, register, or flush Domain Name System (DNS) names. Answer C is incorrect. TRACERT is a route- tracing Windows utility that displays the path an IP packet takes to reach the destination. It shows the Fully Qualified Domain Name (FQDN) and the IP address of each gateway along the route to the remote host.
NEW QUESTION 16
John works as a professional Ethical Hacker. He is assigned a project to test the security of www.we-are-secure.com. He is working on the Linux operating system. He wants to sniff the we-are-secure network and intercept a conversation between two employees of the company through session hijacking. Which of the following tools will John use to accomplish the task?
- A. IPChains
- B. Tripwire
- C. Hunt
- D. Ethercap
Answer: C
Explanation:
In such a scenario, John will use Hunt which is capable of performing both the hacking techniques, sniffing and session hijacking. Answer D is incorrect. Ethercap is a network sniffer and packet generator. It may be an option, but John wants to do session hijacking as well. Hence, he will not use Ethercap. Answer A is incorrect. IPChains is a firewall. Answer B is incorrect. Tripwire is a file and directory integrity checker.
NEW QUESTION 17
You have purchased a laptop that runs Windows Vista Home Premium. You want to protect your computer from malicious applications, such as spyware, while connecting to the Internet. You configure Windows Defender on your laptop to schedule scan daily at 2 AM as shown in the image below: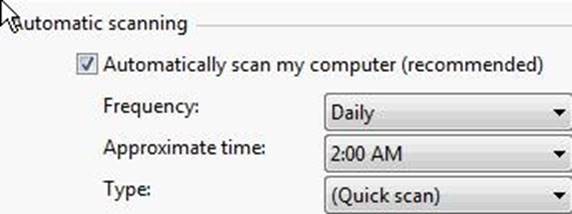
You want Windows Defender to scan the laptop for all the known spyware and other potentially unwanted software, including the latest one. You do not want to manually perform this task. Which of the following actions will you perform to accomplish the task?
- A. Create a scheduled task to download definition files for Windows Defender every Sunday.
- B. Configure Windows Defender to use the definition file placed on the Microsoft Update site for scanning the laptop.
- C. Select the Check for updated definitions before scanning check box in the Automatic Scanning section.
- D. Click the arrow beside the Help button Click the Check for updates option.
Answer: C
Explanation:
According to the question, Windows Defender should scan the laptop for all the known spyware and other potentially unwanted software, including the latest one. Windows Defender uses definitions to scan the system. Definitions are files that include the information of known spyware and potentially unwanted software. To scan a computer for the latest spyware, Windows Defender requires the latest definition files available on the Internet. For this, you have to configure Windows Defender to check for the latest definitions and download them, if available, before scanning the computer. Furthermore, the question also states that the task must be performed automatically. In order to accomplish the task, you will have to select the Check for updated definitions before scanning check box in the Automatic Scanning section.
NEW QUESTION 18
......
P.S. Easily pass GSNA Exam with 368 Q&As Thedumpscentre.com Dumps & pdf Version, Welcome to Download the Newest Thedumpscentre.com GSNA Dumps: https://www.thedumpscentre.com/GSNA-dumps/ (368 New Questions)
- Top Tips Of Rebirth GSNA Exam Question
- Leading GIAC Systems And Network Auditor GSNA Braindumps
- Update GCIA Free Exam For GIAC Certified Intrusion Analyst Certification
- How Many Questions Of GSNA Braindumps
- The Secret Of GIAC GSNA Training
- All About Actual GSNA Study Guides
- Validated GIAC GISF Practice Question Online
- How Many Questions Of GISF Training Materials
- Highest Quality GIAC GCIH Dump Online
- Avant-garde GIAC Certified Incident Handler GCIH Exam Prep

